API Keys and Service Accounts: The Untracked Highway Into SaaS
Anand Kumar · April 11, 2026
Humans use SSO; machines use keys. Explore how API keys and service principals create invisible long-lived access to SaaS—and how to inventory and rotate them before attackers do.
Employee offboarding workflows terminate SSO sessions and reclaim licenses; they rarely touch API keys embedded in cron jobs, serverless functions, or CI pipelines. Service accounts often outlive the projects that created them, silently renewing OAuth grants with broad scopes. For attackers, these credentials are high value: they bypass MFA and rarely appear in user activity reports.
Discovery approaches
Start with your cloud identity provider’s application registrations and OAuth grants. Export service principals and their permission scopes. Correlate to repositories scanning for hard-coded secrets—many keys leak into Git history despite policies. For major SaaS APIs, use vendor consoles to list active tokens and IP restrictions where available.
Hardening patterns
Prefer short-lived tokens over static keys where platforms allow. Scope OAuth grants to minimum necessary APIs. Centralize secrets in vaults with rotation policies and audit logs. Tag each non-human identity to an owning team and service—if ownership is unknown, treat the credential as incident-ready.
Bridging security and engineering
Security mandates alone fail without developer-friendly paths. Provide templates, Terraform modules, and fast approvals for compliant patterns. Measure reduction in unknown long-lived keys quarter over quarter; celebrate teams that migrate first.
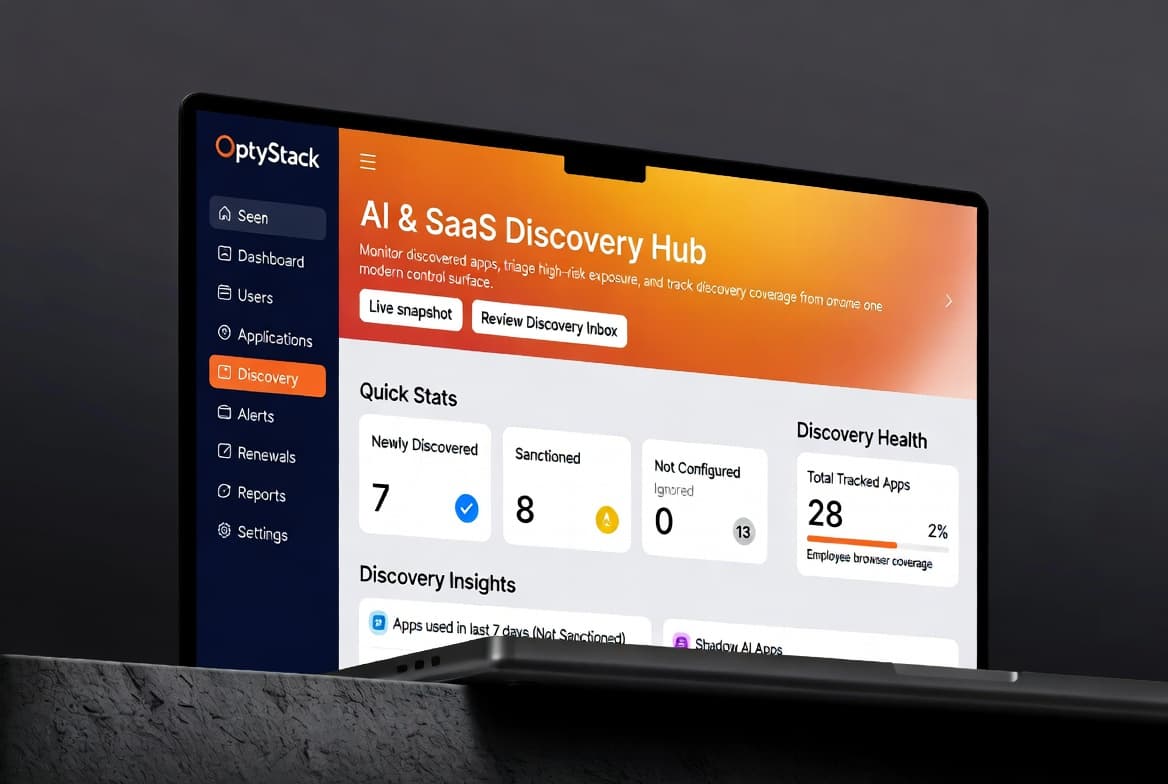
OptyStack helps organizations contextualize SaaS sprawl alongside technical access paths—so human and machine identities become part of one governance story, not two blind spots.
Incident readiness
Assume keys will leak; design for fast revocation. Run tabletop exercises that include rotating OAuth grants and invalidating long-lived tokens. When an incident occurs, pre-mapped ownership and scoped credentials shrink blast radius and recovery time. Post-incident, feed lessons into your discovery backlog—often the compromised path was invisible until it was too late.