Reducing Risk When You Cannot Block Every Unsanctioned App
Ram Kumar · March 28, 2026

Blocking is not always possible. Learn compensating controls: data loss prevention, access reviews, encryption requirements, and phased migration off high-risk shadow tools.
Security teams often want to block unsanctioned applications immediately. Business reality—customer deadlines, inherited stacks, or regional autonomy—means you need a spectrum of responses beyond binary allow/deny.
Prioritize by materiality
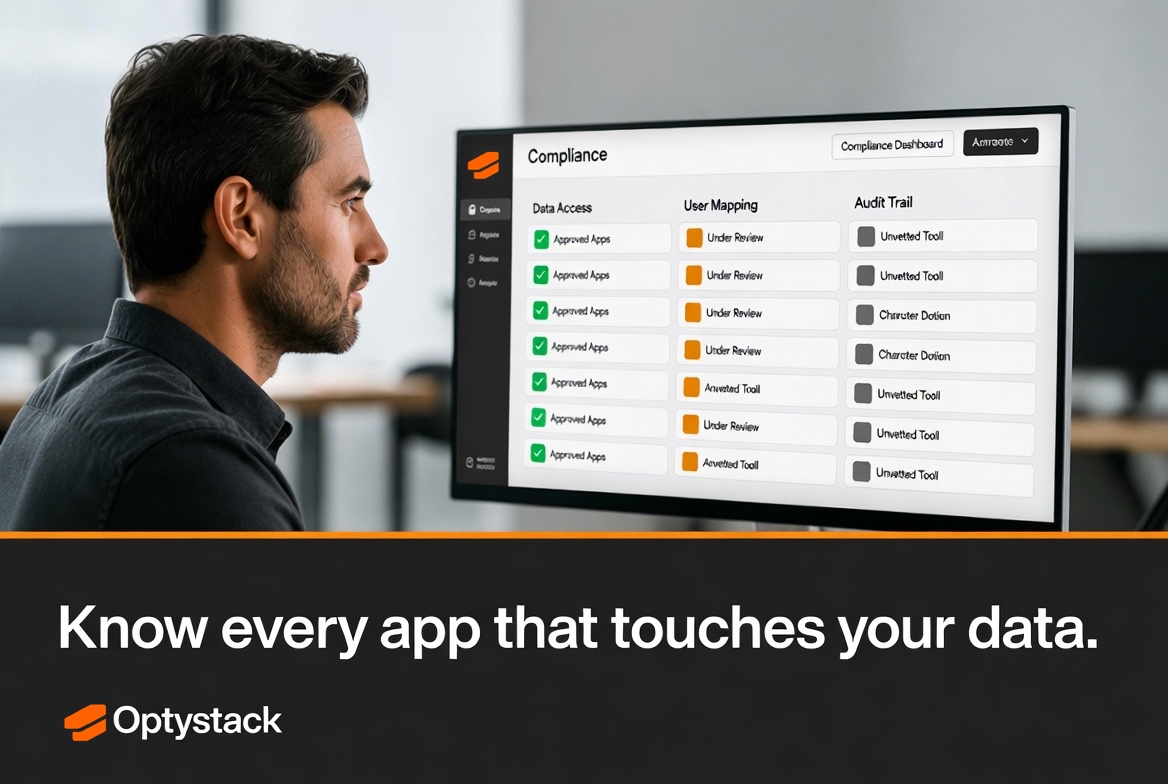
Focus on applications that process regulated data, have broad OAuth access, or integrate with source code and customer records. Lower-priority shadow tools can go into a watchlist with periodic review rather than emergency escalation.
Compensating controls
Where you cannot remove an app overnight, enforce MFA via IdP where possible, tighten DLP rules for uploads to unknown domains, and require annual access certifications for connected identities. Document exceptions with expiry dates so “temporary” does not become permanent.
Migration and consolidation
Offer a sanctioned alternative with migration assistance. Measure duplicate functionality—two project tools or three chat apps—and drive consolidation with clear savings narratives for finance.
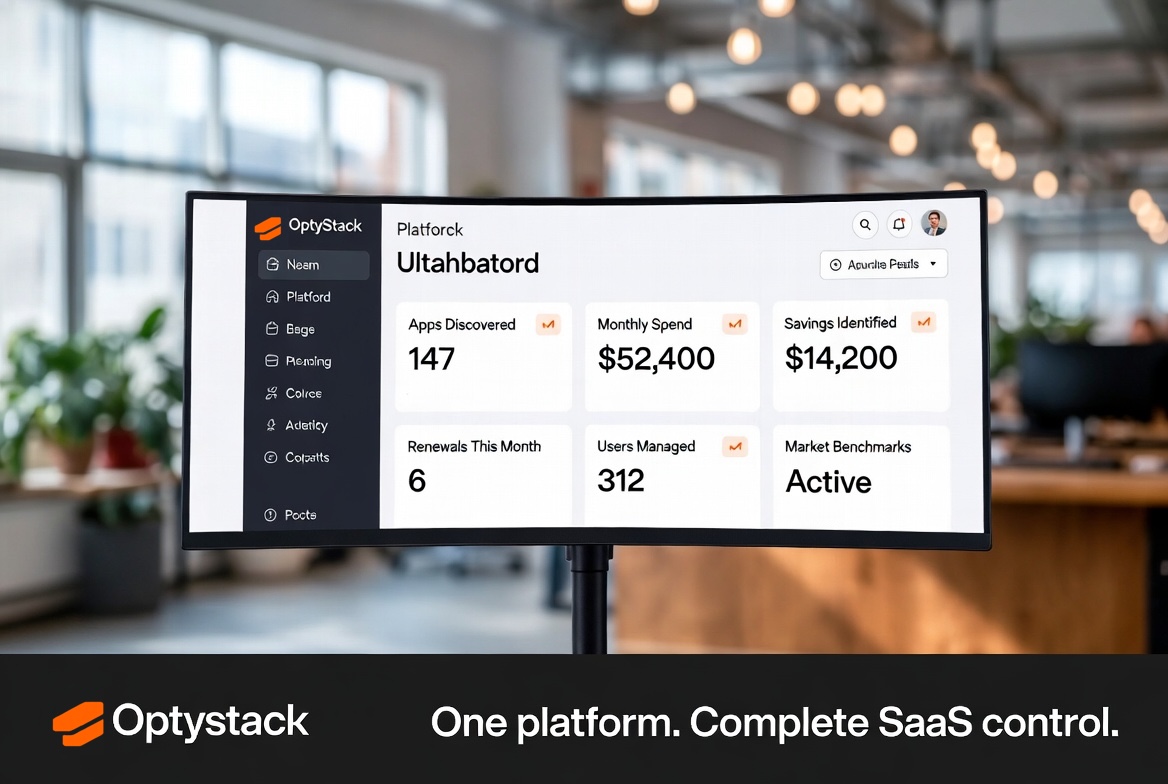
Continuous discovery ensures you revisit controls as usage changes; OptyStack helps track which shadow applications remain open risks versus resolved.