Browser Extensions in the Enterprise: Security Risk and Inventory Tactics
Anand Kumar · April 6, 2026
Extensions can exfiltrate page content and credentials. Learn how security teams inventory browser add-ons, separate benign productivity helpers from high-risk data access, and partner with IT without blocking every install.
Modern work happens in the browser. Extensions that summarize pages, check grammar, or inject AI assistance are one click away—and many request broad permissions that mirror the sensitivity of the sites employees visit. Security teams cannot treat extensions as trivia; they are executable code with access to SSO sessions, customer support portals, and internal admin consoles.
Classify by permission, not by brand
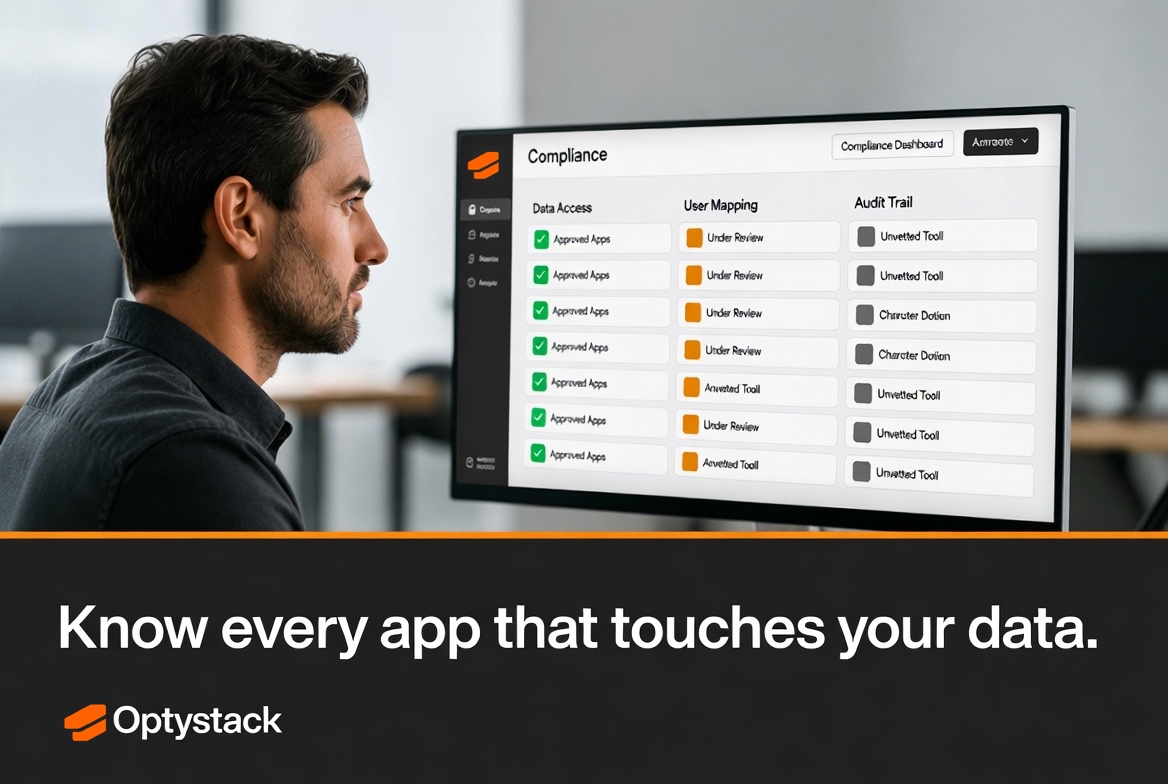
A well-known brand name does not guarantee least privilege. Review manifests for permissions like “read and change all your data on all websites” or broad clipboard access. High-risk extensions warrant allowlisting only after security review; medium-risk may be available in a managed catalog; low-risk productivity aids can be self-service with telemetry.
Where enterprise browsers support extension policies, enforce separation: development environments may allow broader experimentation; customer-facing roles get stricter defaults.
Operational discovery
Endpoint management and browser management tools can report installed extensions, but coverage varies by OS and BYOD policy. Combine those signals with network and CASB visibility where available. The goal is not perfection on day one—it is trending down unknowns quarter over quarter.
Partnering with employees
Blanket bans drive shadow behavior. Publish a short request path for new extensions, with SLAs that respect business deadlines. When you remove a risky add-on, point users to an approved alternative. Communication turns enforcement into partnership.
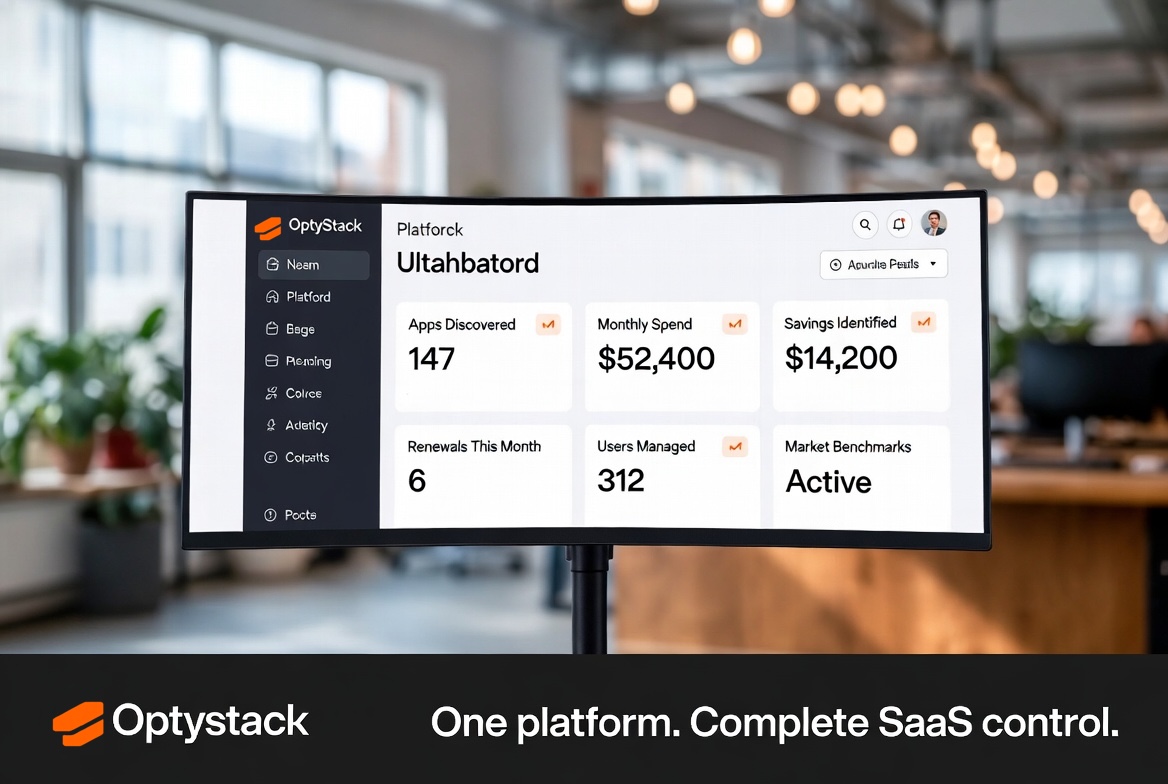
OptyStack complements technical controls by highlighting unsanctioned SaaS and AI surfaces—including long-tail browser tools—so security and IT leaders prioritize what matters most.
Metrics and maturity
Track coverage percentage: devices or browsers where you have extension visibility, and trend unknowns downward. Pair with incident retrospectives—when data leaves through an extension, trace whether policy, tooling, or training failed. Mature programs review the allowlist quarterly and retire vendors that no longer justify their permission footprint.