How MDM and UEM Signals Complement Application Discovery
Sahil Singh

Devices tell you what is installed; identity tells you who signed in. Combine MDM/UEM inventory with IdP and spend data for a fuller picture of SaaS sprawl on endpoints.
Mobile device management and unified endpoint management excel at installed software: thick clients, VPN profiles, and managed browsers. SaaS discovery excels at subscriptions accessed purely through the web. Neither alone captures the full stack employees use—together, they are stronger than the sum of their parts.
What MDM/UEM adds
Agents reveal thick-client SaaS (think design tools, IDEs with cloud backends) and version drift that SSO never sees. They also expose sideloaded or unsigned apps on managed devices—often precursors to shadow SaaS workflows. Correlating device user to corporate identity links those installs to cost centers and managers.
Where MDM/UEM falls short
Browser-only SaaS and personal-device access bypass traditional agents. BYOD policies may intentionally limit visibility. That is why pairing endpoint telemetry with identity, network, and spend signals remains necessary. Treat each source as probabilistic evidence, not absolute truth.
Integration patterns
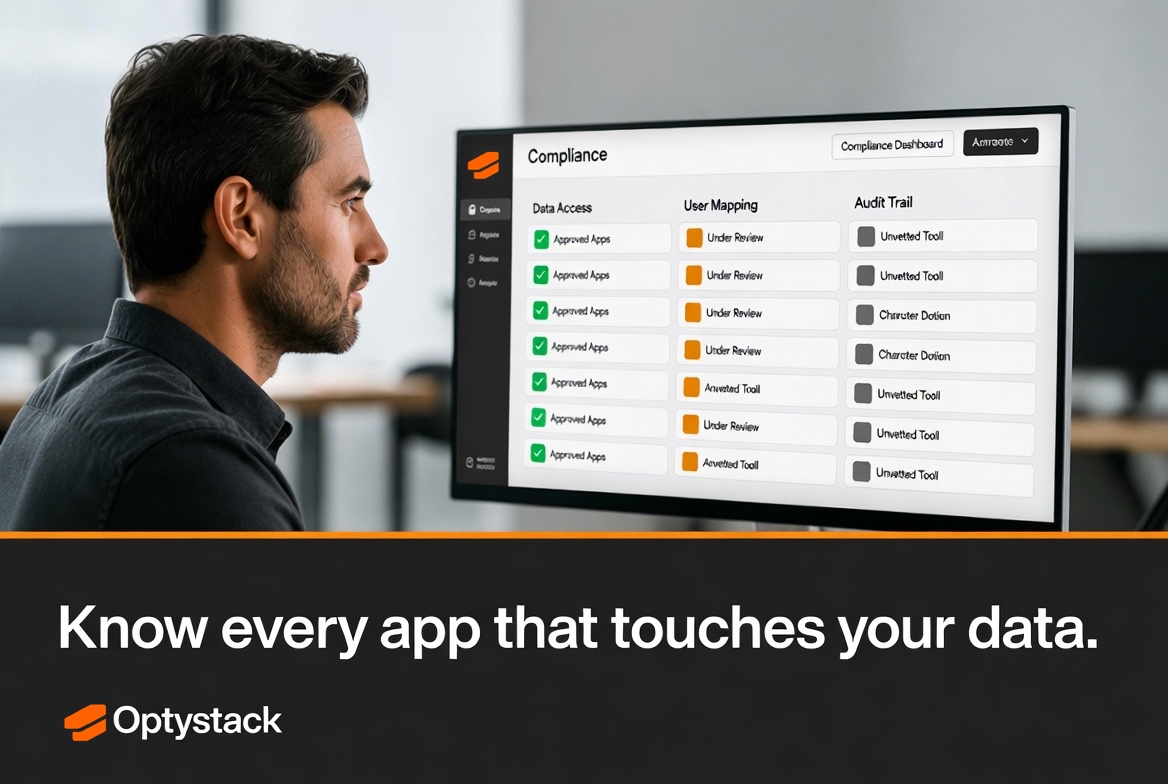
Export device application inventories weekly into your discovery platform. Deduplicate against known sanctioned bundles. Flag high-risk categories—file sync, screen capture, unknown AI assistants—for security review. Over time, tune alert thresholds to reduce noise.
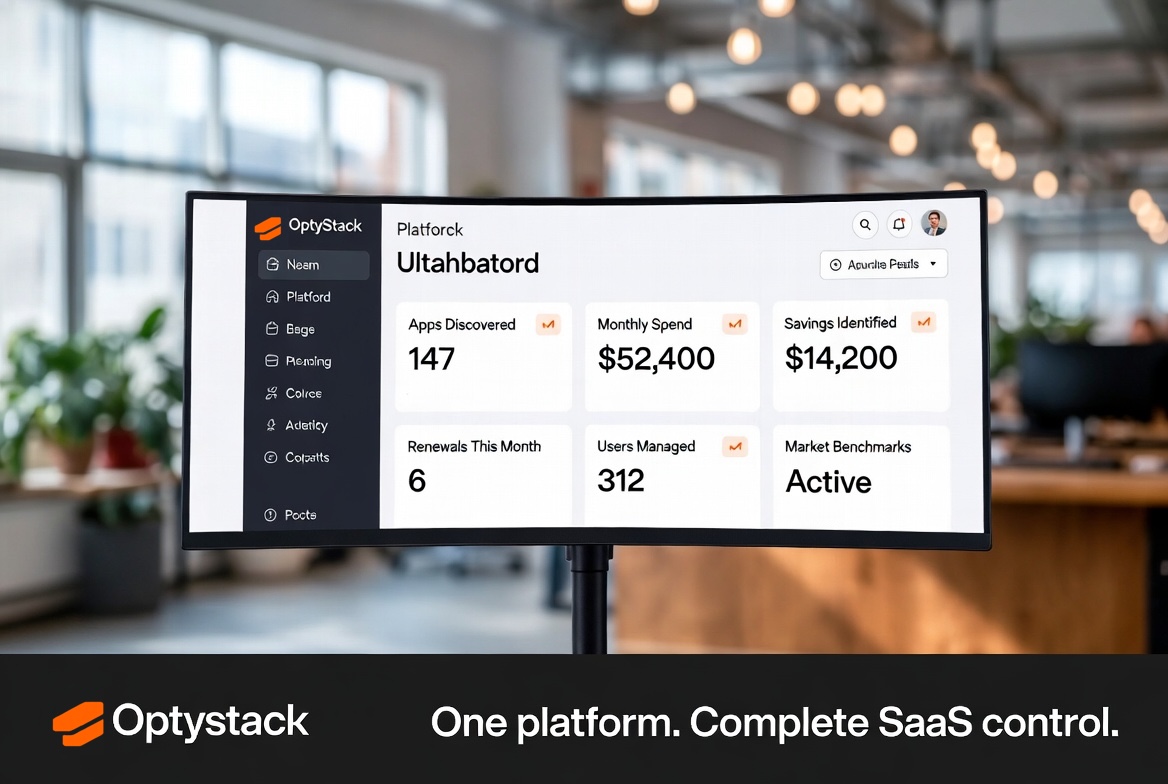
OptyStack fits into this architecture as the aggregation and prioritization layer—turning multi-source noise into an actionable SaaS portfolio view.
Governance without gridlock
Balance thoroughness with employee experience. Heavy-handed blocking of legitimate installers fuels workarounds. Publish clear criteria for exceptions and measure turnaround time. When MDM shows a risky app alongside SSO showing enterprise adoption of the same vendor under a different path, merge the story—duplication often means confusion, not malice.