Taming the Beast: The Hidden Security Risks of Unmanaged SaaS
Amit Dangi · March 10, 2026

When employees bypass IT to use unvetted SaaS tools, they unknowingly open the door to devastating data breaches. Learn how loose OAuth permissions, weak authentication, and compliance black holes make "Shadow IT" the biggest threat to your corporate data security—and how to regain control of your ecosystem.
For decades, the standard IT security strategy was simple: build a massive wall. We protected the corporate perimeter with physical firewalls, VPNs, and on-premise servers. We inherently trusted devices inside the network and blocked everything on the outside.
Today, that perimeter no longer exists.
Your critical corporate data does not live safely within a climate-controlled server room down the hall. It is scattered across hundreds of third-party cloud servers, accessed by remote employees on personal networks, and managed by vendors your IT department has likely never vetted.
The widespread adoption of cloud software has driven incredible productivity, but it has also spawned a dangerous new class of security liabilities: Unmanaged SaaS.
The Disappearing Perimeter and the Rise of Shadow IT
Unmanaged SaaS—commonly referred to as Shadow IT—occurs when employees or entire departments adopt software outside of the approved IT procurement channel.
Why does this happen? Because modern software is designed to bypass IT. Product-Led Growth (PLG) strategies allow a marketing manager to simply input a corporate credit card, or even just sign up for a freemium account, and instantly start uploading proprietary company data into a new tool.
When an application is unmanaged, IT has zero visibility into its security posture, its data handling practices, or who has access to it. You cannot secure what you cannot see.
This lack of oversight introduces three critical, hidden weights to your organization's risk profile:
1. Overscoped OAuth Permissions (The Silent Data Leak)
This is arguably the most insidious threat in the modern SaaS landscape.
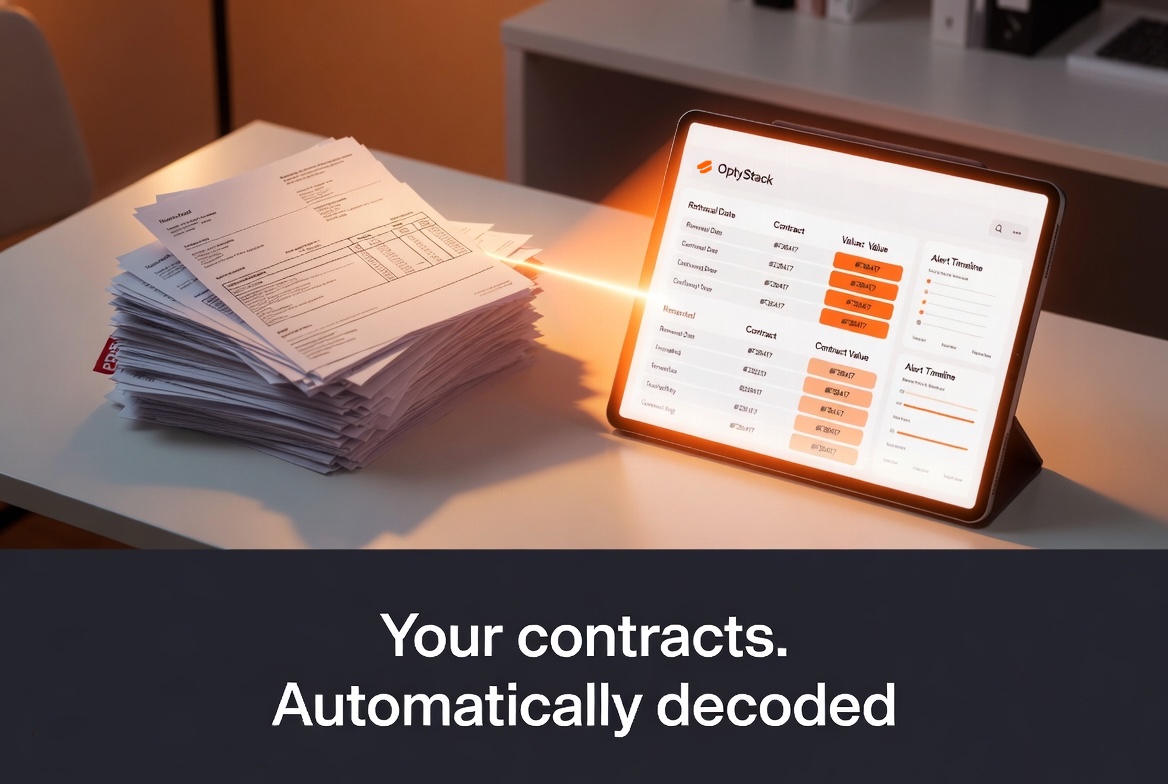
When an employee signs up for a new, unvetted web app—let's say an AI scheduling assistant or a PDF converter—they are often prompted to "Sign in with Google" or "Sign in with Microsoft."
To make the app work, the employee clicks "Allow" on a pop-up requesting permissions (OAuth scopes). Most users never read these. They unknowingly grant a third-party, potentially insecure application full Read/Write/Delete access to their entire corporate inbox, calendar, and cloud drive.
If that obscure PDF converter is breached, the hackers don't just get the employee's password; they get a direct, authenticated API token into your company's core communication infrastructure. Your proprietary code, financial documents, and customer communications are now exposed, completely bypassing your traditional security measures.
2. Weak Authentication and the Credential Reuse Trap
When IT manages an application, they enforce Enterprise Single Sign-On (SSO) and robust Multi-Factor Authentication (MFA). When employees manage their own Shadow IT apps, security best practices go out the window.
Unmanaged applications almost never sit behind your corporate Okta or Azure AD instance. Instead, they rely on standalone usernames and passwords. Human nature dictates that employees will reuse the same weak passwords across multiple sites.
If an employee uses a variation of their corporate password for a free, unvetted project management tool, and that tool is compromised, attackers will immediately test those credentials against your core corporate systems in a "credential stuffing" attack. A breach in a low-level Shadow IT app frequently becomes the skeleton key to your entire kingdom.
3. The Compliance and Legal Black Hole
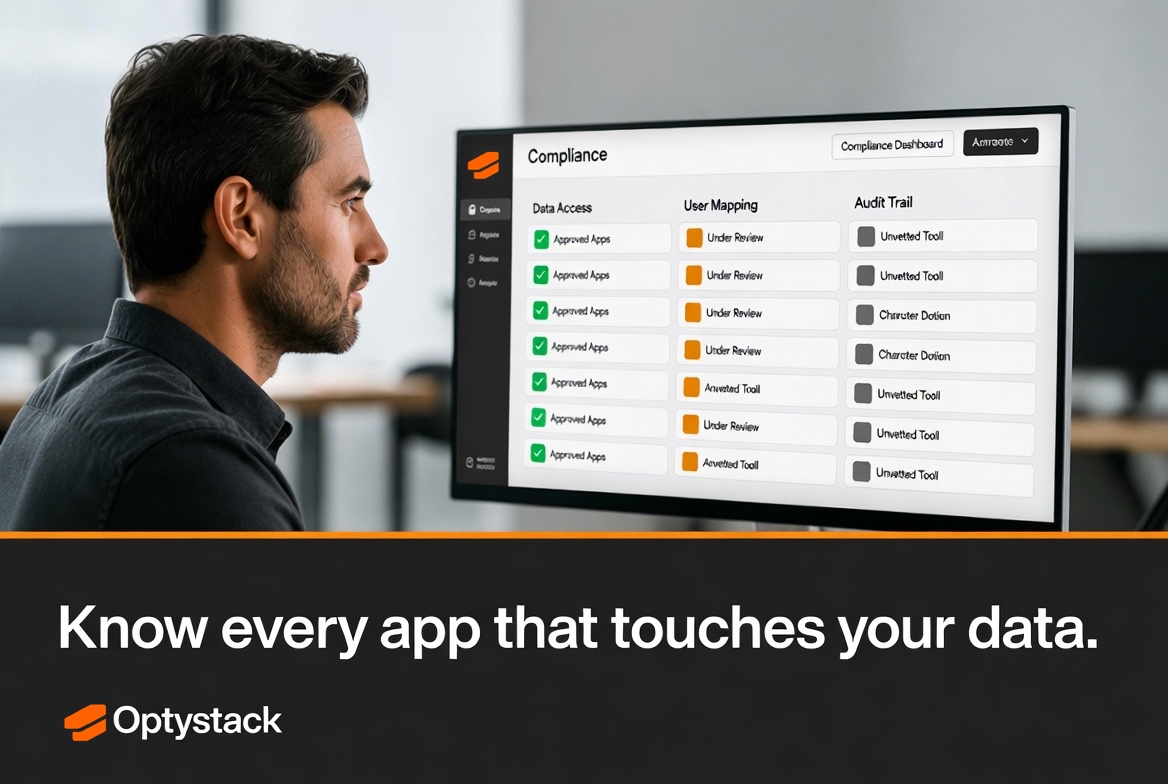
Data privacy is no longer just a best practice; it is the law. If your organization is bound by regulations like GDPR, CCPA, HIPAA, or SOC 2, you are legally responsible for tracking exactly where your data goes and how it is secured.
When sensitive customer Personally Identifiable Information (PII) is uploaded to an unmanaged SaaS application, you have instantly failed your compliance mandates.
Has this vendor signed a Data Processing Agreement (DPA)?
Is their data encrypted at rest?
Do they have a breach notification protocol?
With Unmanaged SaaS, the answer to all these questions is: We don't know. This ignorance is not a legal defense; it is a fast track to massive regulatory fines, loss of customer trust, and severe reputational damage.
Lighting Up the Shadows: The Path to Governance
The instinctive IT reaction to Shadow IT is often draconian: block domains, lock down devices, and ban unapproved apps. But in the modern workplace, banning SaaS is like trying to hold back the tide. Employees will simply find workarounds, driving the risky behavior further underground.
The actual solution is Visibility and Governance.
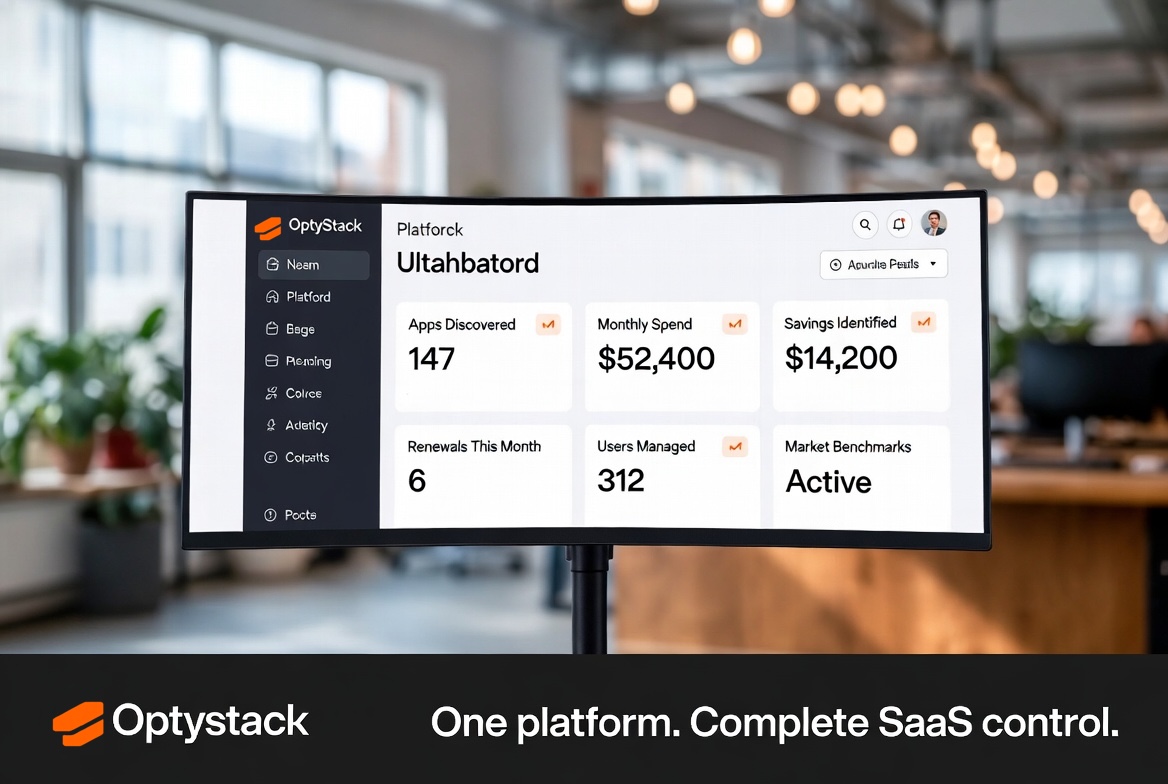
You must transition from being a blind gatekeeper to an informed orchestrator. This requires deploying a SaaS Management Platform that can:
Discover every application active in your environment by analyzing SSO logs, financial integrations, and browser extensions.
Audit third-party OAuth connections and automatically revoke risky, overscoped permissions.
Consolidate decentralized tools behind your central Identity Provider to enforce MFA and strict access controls.
Taming the beast of Unmanaged SaaS doesn't mean stopping innovation. It means giving your employees the tools they need to move fast, while giving IT the visibility required to ensure they do it safely.