Identity Governance for SaaS: Provisioning, Segregation of Duties, and the Limits of SSO Alone
Marcus Chen · April 15, 2026

SSO is necessary but not sufficient for governance. Explore how role design, emergency access, SoD rules, and periodic access reviews interact with SaaS admin models—and where identity teams should instrument compensating controls.
Single sign-on gave enterprises a front door to sanctioned applications, but the rooms inside still have their own permission models. A finance user authenticated through your IdP can still become a workspace admin inside a collaboration tool, approve their own expenses in an adjacent SaaS, or create API tokens with broader scopes than any on-premises role would allow. Identity governance for SaaS must therefore span federation, application-native roles, and the business processes those roles touch. When teams assume SSO equals governance, auditors find segregation-of-duty violations that no amount of SAML hardening will prevent.
Map roles to business functions
Start by translating coarse directory groups into meaningful application personas. “Employees-All” is convenient for licensing but useless for SoD analysis. Instead, define role bundles aligned to tasks: invoice approver, tenant configurator, support agent with PII access. Document which combinations are toxic—for example, the same person should not configure payment rails and approve disbursements without a compensating control such as dual control workflows inside the SaaS.
Many SaaS products lack granular entitlements; you may need process controls when technical enforcement is impossible. Publish those exceptions explicitly so internal audit can test them. Hiding limitations behind vague “we use SSO” language invites findings.
Provisioning and lifecycle
Joiner-mover-leaver automation through SCIM reduces latency and human error, but only if attribute sources are authoritative. HR systems that lag real-world manager changes will propagate wrong approvers into SaaS until the next sync. Implement reconciliation jobs that compare IdP groups to application rosters and flag drift. For high-risk apps, require periodic attestation even when automation is perfect—because business context changes faster than attributes.
Emergency access (“break glass”) accounts need tight time bounds, MFA, session recording where feasible, and post-incident review. Without those guardrails, privileged SaaS admins become permanent backdoors. Pair technical controls with culture: reward teams that document emergency usage promptly instead of punishing them for needing access during outages.
Access reviews that people actually finish
Quarterly certification campaigns fail when reviewers face thousand-row spreadsheets unrelated to their teams. Scope reviews by data sensitivity and manager hierarchy; show usage signals so reviewers can distinguish active accounts from dormant ones. Auto-revoke obvious stale accounts after grace periods with clear communication. The goal is risk reduction, not checkbox exhaustion.
- Service accounts — Treat non-human identities like privileged users; rotate secrets and map owners.
- OAuth grants — Users authorize third-party apps with scopes that bypass your RBAC model; include grants in discovery.
- Contractors — Time-bound access with automatic expiry reduces forgotten externals with lingering admin rights.
Bridging IAM and FinOps signals
Provisioning decisions affect cost: every extra seat in a tiered product triggers incremental spend. When identity and FinOps share dashboards, managers see that approving an access request has budget impact, not just security impact. That alignment prevents the all-too-common pattern where finance cuts licenses while IT never removes corresponding entitlements—or vice versa.
Privileged paths in SaaS admin consoles
Application administrators often hold superuser capabilities that bypass SSO session policies—impersonation, support-mode access, and bulk exports. Treat those accounts like infrastructure root: MFA hardening, just-in-time elevation, and session recording where vendors support it. Review admin role assignments quarterly; long-tenured admins accumulate rights across modules they no longer operate.
Document break-glass procedures for SaaS outages separately from directory outages. Teams sometimes disable SSO during incidents and revert to local passwords; ensure those credentials rotate immediately after recovery and that audit logs capture the window.
Federation edge cases
Linked accounts, social logins, and vendor-side “backup emails” create alternate authentication paths that SoD reviews miss. Periodically audit for users who can authenticate without your IdP. Where vendors allow it, disable password logins entirely for enterprise domains. Where they do not, compensate with phishing-resistant MFA mandates and monitoring for impossible travel on local accounts.
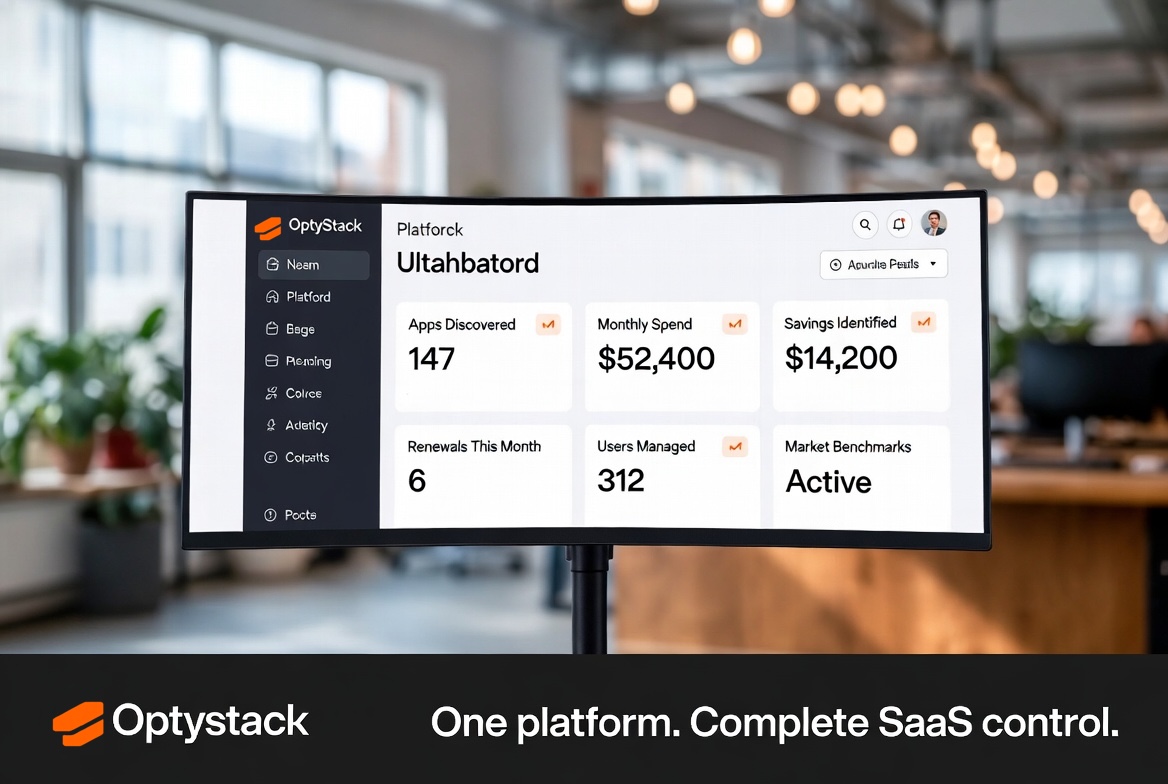
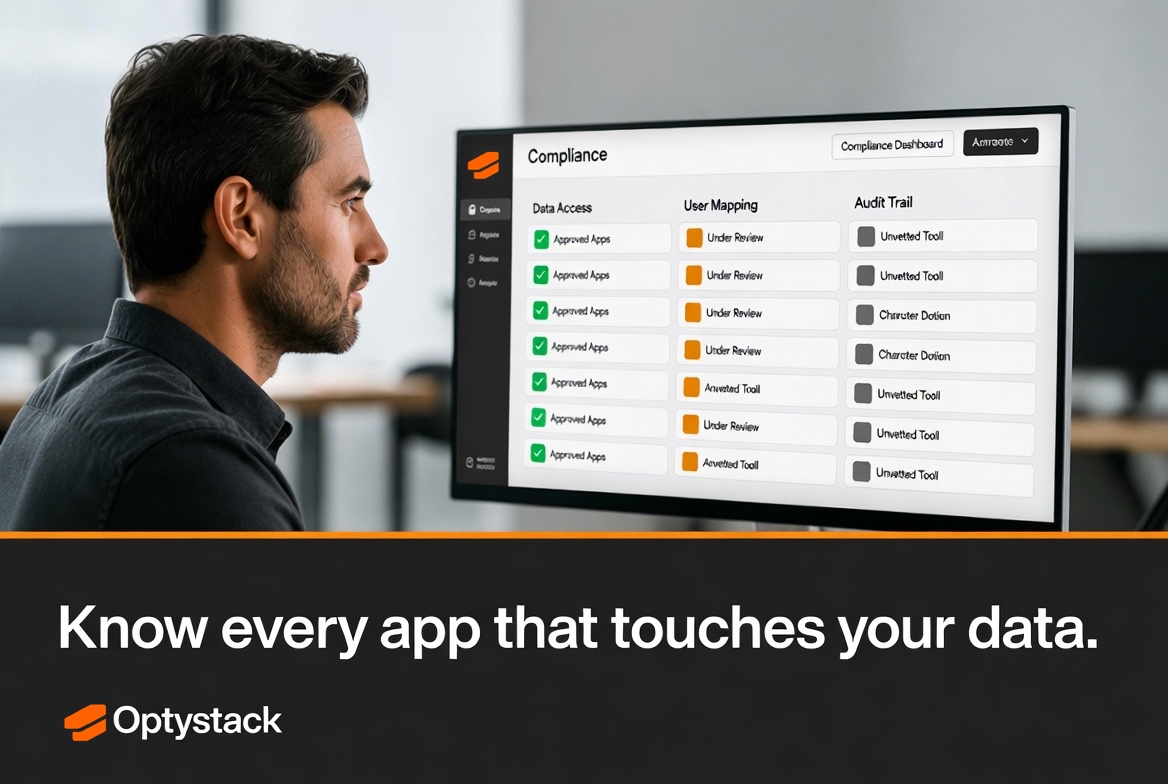
OptyStack complements identity investments by revealing which SaaS applications are active, how users authenticate, and where admin roles concentrate outside traditional directories. Combining those signals with IGA workflows closes the gap between “authenticated” and “appropriately authorized.”
Operating model
Assign clear ownership: IAM engineering maintains standards and integrations; application administrators enforce native role policies; internal audit samples high-risk combinations. Meet monthly to review incidents, policy exceptions, and upcoming SaaS launches. Governance matures when conversations are proactive instead of triggered only by findings.
SSO was the first chapter of SaaS identity; governance is the rest of the book. Organizations that invest in roles, lifecycle, and evidence win not only compliance—they gain faster, safer adoption of new tools because employees trust the system that grants access.
Machine identities and SaaS-to-SaaS trust
Service principals that call other SaaS APIs create trust chains invisible to traditional user-centric SoD reviews. Inventory OAuth client IDs, webhook secrets, and cross-app automation recipes the same way you inventory human admins. When a marketing automation platform can push records into a CRM and a data warehouse concurrently, separation of duties must span those hops—not stop at each UI.
Require owners for every non-human identity with quarterly attestation. Rotate credentials automatically where APIs allow; where they do not, track vendor roadmaps and escalate risk acceptance when manual rotation is quarterly at best.
Board and regulator storytelling
When leadership asks whether identity risk is “under control,” answer with trend metrics: reduction in toxic role combinations, faster deprovisioning after HR events, and fewer emergency admin grants. Narratives grounded in measurable identity hygiene resonate more than assertions about SSO coverage alone.
From policy to sustainable operations
Publish reference architectures for common SaaS patterns—SSO-only, SCIM-provisioned, API-led—so engineers do not improvise insecure shortcuts. Reference architectures should include approved configuration snippets and test cases identity teams validate in staging tenants before production rollout.
Invest in synthetic monitoring of critical authentication flows. SSO outages strand employees silently; proactive checks detect certificate expirations and misconfigured redirect URLs before Monday morning volume spikes. Pair technical monitoring with comms templates so help desks respond consistently.
When auditors sample access, provide them curated evidence packages: policy PDFs, configuration exports, and ticket trails—not raw log dumps they must interpret. Curated packages shorten audits and reduce misinterpretation risk.
Finally, celebrate teams that retire toxic combinations voluntarily. Incentives matter: recognition in operational reviews costs nothing but reinforces that governance is a shared success metric, not a security-only KPI.
Scaling identity governance globally
Regional privacy laws affect what attributes you may store in global identity profiles and which audit logs you can centralize. Design IGA processes that respect data minimization per region while still giving security a coherent enterprise view. Sometimes regional IdP shards with federated trust beat a forced global directory that violates local rules.
Provide localized training materials and office hours; identity mistakes often stem from misunderstanding, not resistance. Measure ticket volume and time-to-provision by region to detect where friction concentrates.
Plan for vendor-side outages: maintain cached critical group memberships and break-glass instructions per region so a single SaaS admin console outage does not freeze productivity worldwide.
Key takeaways
SSO is the front door; roles, reviews, and machine identities are the rooms. Invest in measurable outcomes—fewer toxic combinations, faster offboarding, clearer emergency access—rather than checkbox coverage. Partner FinOps with IAM so every access decision reflects both risk and cost. Tell leadership stories anchored in trends, not anecdotes. Global programs need regional nuance, localized training, and resilient playbooks when cloud dependencies wobble.
Small, consistent improvements in identity hygiene outperform one-time “big bang” cleanups that revert within a quarter.