How SSO and Identity Telemetry Reveal Hidden SaaS Usage
Ram Kumar · March 24, 2026
SSO adoption is uneven. Learn how to combine IdP logs, OAuth grants, and login patterns to find applications employees use outside your golden path—and how to close gaps without hurting productivity.
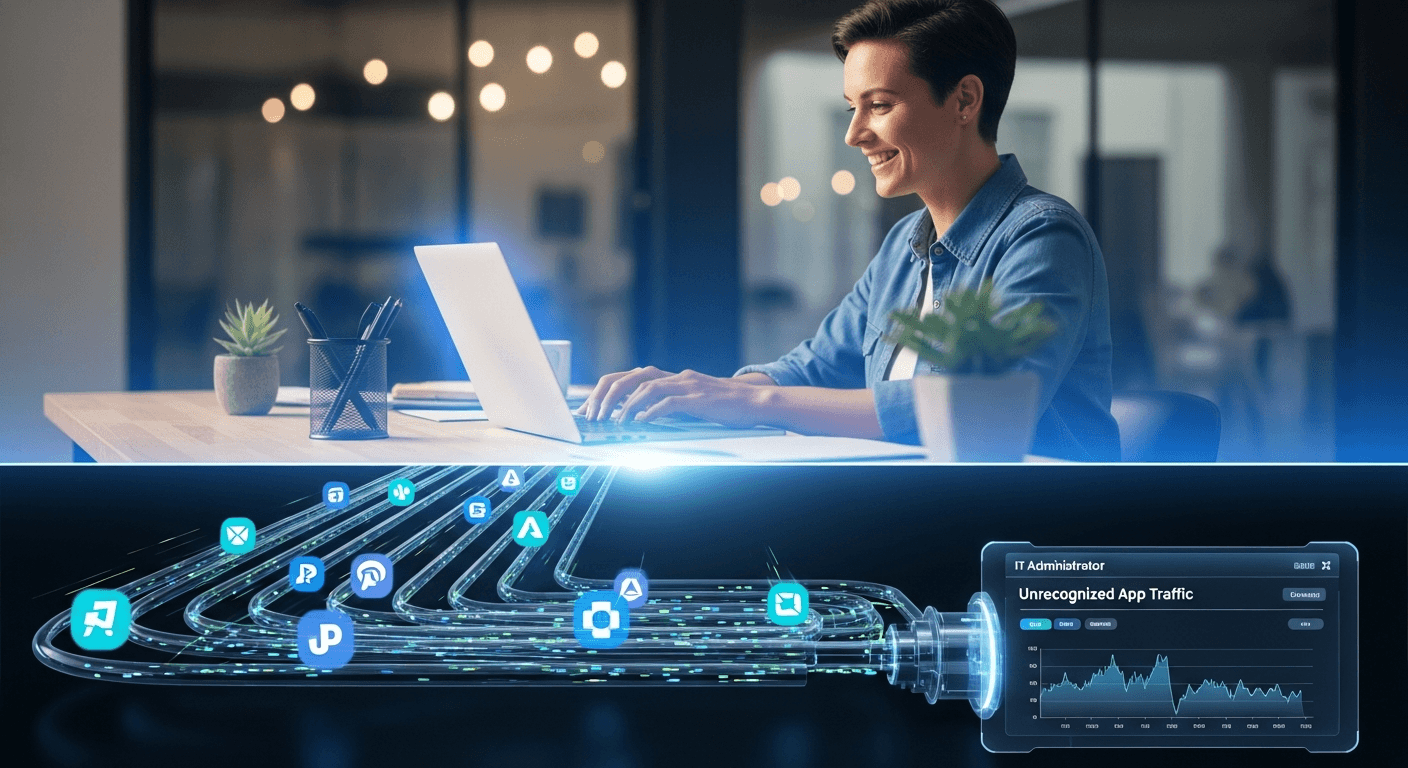
Many organizations assume that mandating SSO for “all business applications” eliminates shadow IT. In practice, employees still authenticate with personal emails, use free tiers, or access tools that only support local accounts. Your identity plane remains the richest signal for what is officially connected if you know how to read it.
What to extract from your IdP
Modern identity providers log application assignments, SAML/OIDC sign-on events, and OAuth consent grants. Each grant ties a user to a third-party API or SaaS vendor. Mining these logs periodically surfaces “approved” apps that never went through security review, and long-tail integrations your CMDB missed.
Correlate application IDs across dev, test, and prod tenants so you do not double-count the same vendor. Tag grants by scope (read-only vs. broad write access) to prioritize reviews for high-privilege connections.
Beyond SSO: the long tail
SSO alone will not show browser-only tools, AI chatbots used without enterprise keys, or vendors that only invoice via card. Pair IdP data with expense feeds and optional browser or CASB signals where policy allows. The combined picture approximates total SaaS surface area far better than SSO in isolation.
Operational tips
Automate weekly exports or API pulls from your IdP into your discovery platform.
Alert when new OAuth scopes appear for categories like CRM, storage, or AI.
Feed deprovision workflows when employees offboard so stale grants do not linger.
Discovery is never “done”; it is a continuous alignment between identity hygiene and business reality. Tools like OptyStack ingest these streams so teams spend time on decisions, not spreadsheet merges.