Shadow IT Explained: Why 85% of Your Company’s Apps Are Unmanaged (And How to Find Them)
Amit Dangi · January 15, 2026
In 2017, the average organization used just 16 SaaS applications. Today, that number has skyrocketed to over 130 apps.
But here is the scary part: If you ask your CIO for a list of those 130 apps, they probably can’t give it to you.
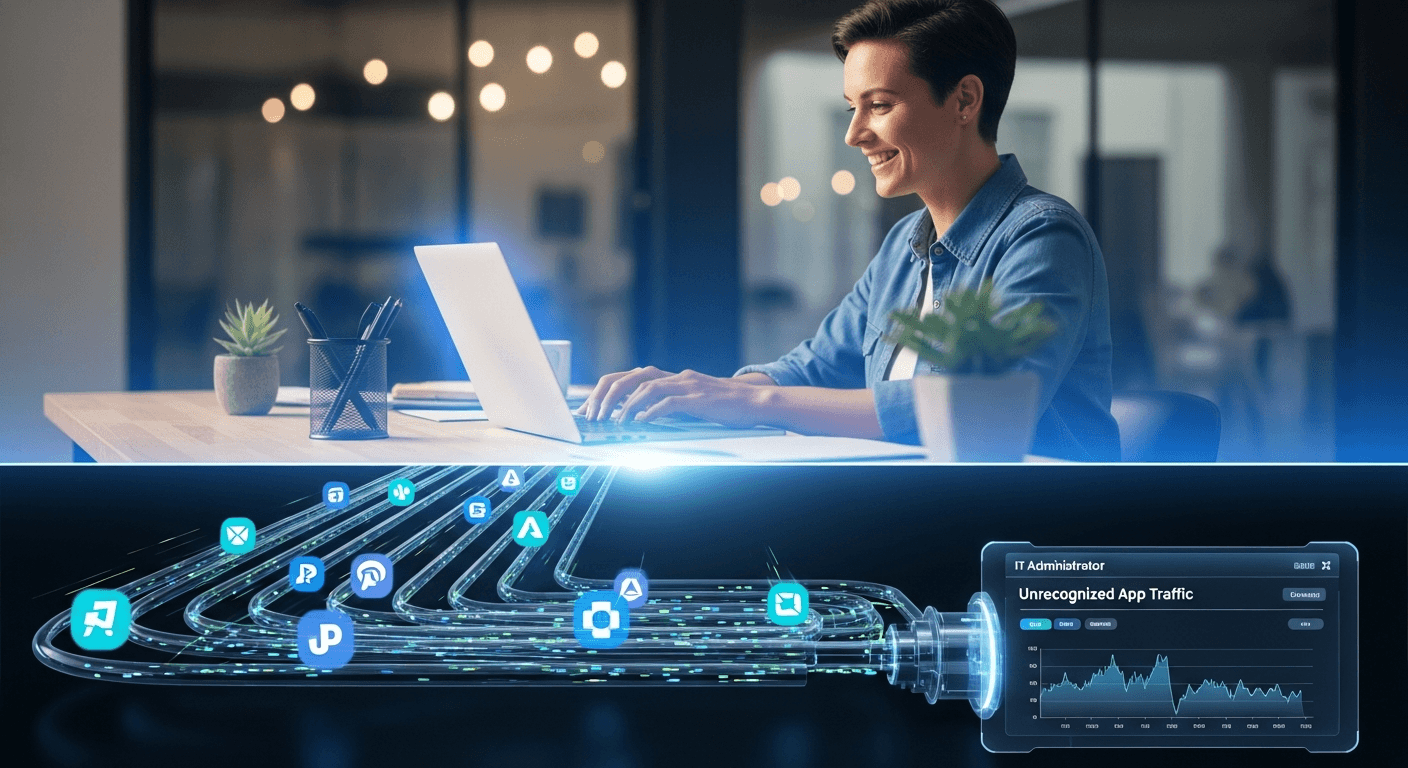
This is the phenomenon of Shadow IT software purchased and deployed by employees outside of formal IT approval processes. Whether it’s a marketing team buying their own project management tool or a developer spinning up a cloud instance on a personal credit card, decentralized purchasing is the new normal.
In fact, data shows that 85% of organizations are currently using SaaS applications that are unknown or unmanaged by their IT department.
If you don’t know what software is running on your network, you can’t secure it, and you certainly can’t optimize what you spend on it.
The Double-Edged Sword: Budget Leaks & Security Risks
Shadow IT isn't just about a few extra dollars on an expense report. It creates two massive liabilities:
1. The "Invisible" Budget Drain When teams buy software in silos, you lose leverage. You might have five different teams paying full price for five different project management tools (Monday, Asana, Trello, etc.) instead of negotiating an enterprise license for one. This fragmentation is a primary reason why organizations waste 30% of their SaaS spend.
2. The Compliance Time Bomb Unmanaged apps are the path of least resistance for hackers. If an employee uploads customer data to an unvetted AI tool or a file-sharing service that IT doesn't know about, you are bypassing your security protocols (SSO, MFA, etc.). This exposes your business to severe compliance risks and potential data breaches.
How to Turn the Lights On
You cannot solve Shadow IT by banning it. Employees buy these tools because they need them to do their jobs. The goal isn't to block innovation, but to gain visibility.
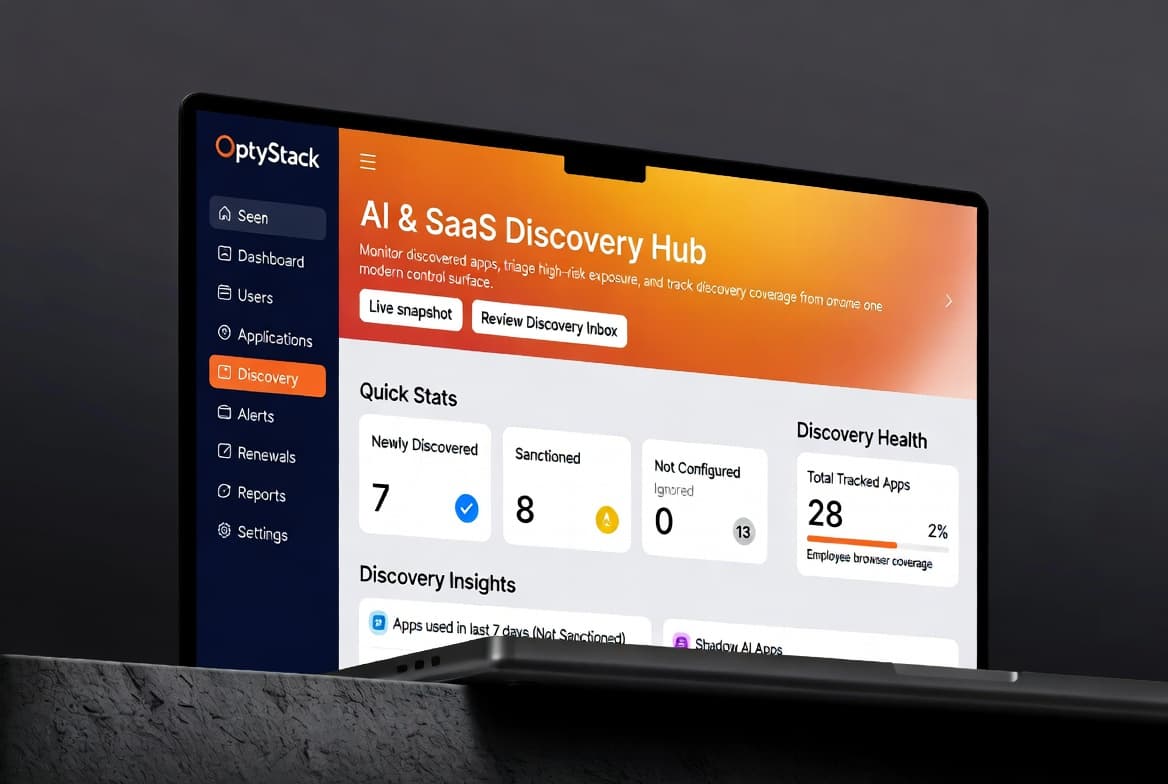
This is where OptyStack comes in. We replace the manual "chasing receipts" method with automated discovery.
• Integrate in Minutes: OptyStack connects securely via OAuth to your core systems Google Workspace, Microsoft 365, and Slack to detect sign-ins and usage patterns.
• Automated Discovery: Our AI scans this activity to identify every application your employees are logging into, cross-referencing it against your approved inventory.
• Single Source of Truth: You get a centralized dashboard showing exactly which apps are in use, who is using them, and where your data is living.
From Chaos to Clarity
Once you have discovered your Shadow IT, you can make informed decisions. Is that unapproved design tool critical for the marketing team? Great let's bring it into the official stack, secure it with SSO and Role-Based Access Controls, and negotiate a better contract. Is it a duplicate tool? Let's migrate those users and cut the cost.
Don't let the "hidden 85%" dictate your security posture or your budget.
[Start your free audit today] and find out exactly what software is running in your organization.